How to enable MFA for VPN
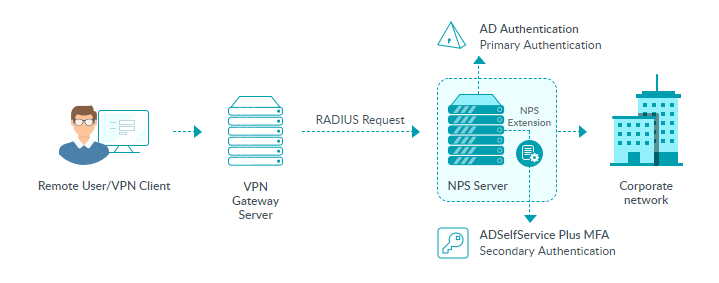
ADSelfService Plus adds additional steps of authentication for VPN logins for enhanced security. To enable MFA for VPN logins, ADSelfService Plus requires the VPN server to use a Windows Network Policy Server (NPS) for authentication. ADSelfservice Plus comes bundled with a NPS extension, which should be installed in the NPS server. This extension facilitates communication between the NPS server and ADSelfService Plus for the MFA during VPN login.
How it works:
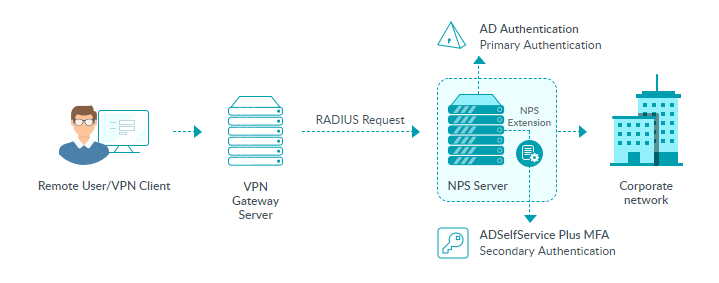
Once the VPN server is configured to use RADIUS authentication, and the NPS extension is installed in the RADIUS server, here is how the authentication process will work:
- A user tries to establish a VPN connection by providing their username and password to the VPN server.
- The VPN server converts the request to a RADIUS Access-Request message and sends it to the NPS server where the ADSelfService Plus’ NPS extension is installed.
- If the username and password combination is correct, the NPS extension triggers a request for second-factor authentication with the ADSelfService Plus server.
- ADSelfService Plus performs the secondary authentication and sends the result to the NPS extension in the NPS server.
- If the authentication is successful, the NPS server sends a RADIUS Access-Accept message to the VPN server.
- The user is granted access to the VPN server and establishes an encrypted tunnel to the internal network.
Configuring MFA for VPN
Prerequisites:
- The Endpoint MFA add-on for ADSelfService Plus is required to enable MFA for VPN and RADIUS-supported endpoint logins. Visit the store to purchase the add-on.
- Configure your VPN or endpoint server to use RADIUS authentication.
- For the RADIUS server, you must use a Windows server (Windows Server 2008 R2 and above) with NPS role enabled.
- Enable HTTPS in ADSelfService Plus (Admin → Product Settings → Connection).
Note: If you are using an untrusted certificate in ADSelfService Plus to enable HTTPS, you must disable the Restrict user access when there is an invalid SSL certificate option in Configuration → Administrative Tools → GINA/Mac/Linux (Ctrl+Alt+Del) →GINA/Mac/Linux Customization → Advanced.
- In Active Directory, set users’ Network Access Permission to Control access through NPS Network Policy in their Dial-in properties.
- The Access URL you have configured in Admin → Product Settings → Connection → Configure Access URL will be used by the NPS extension to communicate with the ADSelfService Plus server. Make sure you have updated the Access URL before installing the NPS extension.
- In the Windows NPS server, where the NPS extension is going to be installed, set the Authentication settings of the Connection Request Policy to Authenticate requests on this sever.
Step 1: Enable the required authenticators
Based on whether the RADIUS client (VPN server) supports RADIUS challenge-response or not, the authentication methods you can enable for VPN logins may vary.
Authenticators supported for endpoint VPN MFA can be classified into:
- One-way authenticators
These authenticators are applicable by default for all the endpoints providing RADIUS authentication.
Note:
- When you enable push notification or Fingerprint/Face ID authentication, make sure the ADSelfService Plus server is reachable by the users (through the internet) from their mobile devices.
- RADIUS authentication timeout should be set to at least 60 seconds in the VPN server's RADIUS authentication configuration settings.
- Challenge-based authenticators
Challenge-based authenticators are applicable only when:
- Password Authentication Protocol (PAP) is configured for the RADIUS authentication method.
- The RADIUS client (VPN or endpoint server) supports challenge-response, that is, it has a way for prompting a challenge (verification code) from the user and sending back the challenge entered by the user.
Note: When challenge-based authenticators are used, the RADIUS attributes that are configured in the network policy won't be forwarded to the RADIUS client (VPN or endpoint server). As a result, the VPN client might either have more access than you want it to have, or less access than it needs, or no access.
Step 2: Enable MFA for VPN in ADSelfService Plus
- Log into ADSelfService Plus as an admin.
- Go to Configuration → Self-Service → Multi-Factor Authentication → MFA for Endpoints.
- Select a policy from the Choose the Policy drop-down. This policy will determine the users for whom MFA for VPN login will be enabled. To learn more about creating an OU or a group-based policy, click here.
- In the MFA for VPN Login section, select the checkbox next to Select the authenticators required. Choose the number of authentication factors to be enforced. Select the authentication methods to be used. The authentication methods listed can also be rearranged by dragging and dropping at the necessary position.
- Click Save Settings.
Step 3: Install the NPS extension
- Log in to ADSelfService Plus as an admin, and go to Configuration > Self-Service > Multi-Factor Authentication > MFA for Endpoints. Download the NPS extension using the link provided in the Notes section.
- Copy the extension file (ADSSPNPSExtension.zip) to the Windows server, which you have configured as the RADIUS server. Extract the ZIP file’s content and save it in a location.
- Open Windows PowerShell(x64) as administrator and navigate to the folder where the ZIP file’s content are located.
-
Execute the following command:
PS C:\> .\setupNpsExtension.ps1 <operation>
where, the operation can by install, uninstall, or update.
Install: installs the NPS extension plugin.
Uninstall: uninstalls the NPS extension plugin.
Update: updates the extension to newer versions and configuration data.
- After installation, you will be prompted to restart the NPS(ias) Windows service. Proceed with the restart.
Advanced settings
Refer to Advanced Settings to configure VPN MFA session limit and the options to bypass MFA if ADSelfService Plus is not reachable or the user is not enrolled.
Enabling MFA for VPN based on connection request policies and network policies
If you have configured connection request policies or network policies in your RADIUS server, you can enforce MFA for VPN login to certain users based on those policies. To do so,
- Open the Registry Editor (type regedit in the Run dialog box).
- Go to HKEY_LOCAL_MACHINE\SOFTWARE\ZOHO Corp\ADSelfService Plus NPS Extension.
Note:
- Take a backup of the registry key before editing it.
- Only the built-in administrator group in the computer will have privilege to edit this key.
- You can customize the properties mentioned below according to your organization's requirements:
- ServerName: Mention the HostName or IP address of the ADSelfService Plus web server.
- ServerPortNo: Mention the TCP port number for the ADSelfService Plus web server.
- ServerContextPath: Mention the web server context (if changed).
- MfaStatus: This can be set to true or false depending on whether you need MFA to be enforced or not.
- ServerSSLValidation: This can be set to true or false. If set to true, it verifies the SSL certificate and hostname when establishing an HTTPS connection from the NPS extension to the ADSelfService Plus server. It is recommended that the property always be set to true for security reasons.
- BypassMFAOnConnectionError (Optional): This property can be set to true or false depending on whether MFA can be bypassed if any connection issue is present during authentication.
- CRPolicies (Optional): This property can be used to enforce MFA only for the user who falls under these connection request policies. Enter the connection request policy's name, and if more than policy has to be mentioned, separate the policy names using semicolons (;).
- NetworkPolicies (Optional): This property can be used to enforce MFA only for the user who falls under these network policies. Enter the network policy's name, and if more than one policy has to be mentioned, separate the policy names by semicolons (;).
Note: When both CRPolicies and NetworkPolicies are configured, an authentication request will be considered for MFA only if both the CRPolicies and NetworkPolicies of the RADIUS request matches with the ones configured. If the policies are not configured, MFA will be enforced for all the successful RADIUS requests sent to the NPS server.
- LogLevel (Optional): This property can be used to determine the intricacy of the logged information on the feature's functioning. The property will be set to Normal by default and can be changed to Debug to additionally log details that will aid with debugging. It is recommended that the property be set to Normal.
- Click OK.